Quantum update 5
Quantum computing isn’t a far‑future threat anymore. It’s accelerating fast, and the cybersecurity world is bracing for impact.
What’s Really Happening — and What You Should Do Next
Quantum computing isn’t a far‑future threat anymore. It’s accelerating fast, and the cybersecurity world is bracing for impact.
Recently, Palo Alto Networks’ CEO predicted that hostile nation‑states could have useful quantum computers by 2029. That’s not just a technical milestone — it’s a warning shot. If vendors expect quantum‑capable adversaries within 4 to 5 years, then quantum‑safe hardware and software upgrades aren’t optional. They’re unavoidable and companies like Palo Alto Networks will benefit greatly.
Palo Alto Networks Q1 Fiscal Year 2026 Earnings Call
The Truth: Nation‑States Already Have Quantum Computers
They’re real, but not powerful enough (yet) for cyberattacks. Governments and major research labs already operate quantum computers — they’re just too weak to break modern encryption or run meaningful attack operations. Think of them as ground-breaking, but not ready to reshape the world. That will change - and fast.
Who Actually Needs to Worry Right Now?
Not everyone. Despite the headlines, most organisations are not on the edge of quantum catastrophe. The key risk today lies with companies running bespoke, internally‑built hardware or software that might rely on vulnerable cryptographic primitives. These systems need careful evaluation and, most likely, replacement over the next 4–5 years.
For everyone else, the transition should be far easier. Many consumer and enterprise products are already on a path to quantum‑safe standards — and vendors will quietly swap components out during normal refresh cycles.
But you do still need a Post‑Quantum Cryptography (PQC) migration plan. The key point here is the risk is yours not your suppliers! You should manage the risk accordingly. For those of you in regulated industries such as finance and insurance you should expect legislation to soon require you to have a PQC plan - this means the decision to do something will have been made for you.
The One Group That Should Be Worried Today
If your encrypted data was stolen in the past and is still sensitive or confidential today? Now’s the time to care.
Attackers are banking stolen data (“harvest now, decrypt later”), waiting for quantum machines powerful enough to crack today’s encryption. When they succeed, expect a fresh wave of extortion attempts using your old stolen files. You should plan you response today, while you have no stress or pressure. Don't simply wait for it to happen then respond - your response will be rushed and ill considered.
The group that this keeps awake at night are nation‑states. They have much larger strategic concerns about their stolen encrypted data which could result in a national security or diplomatic incident.
Good News: Quantum‑Safe Tech Is Already Rolling Out
Take Signal, for example. It’s deploying a major upgrade to its famous protocol: a triple ratchet that includes MLKEM768, a NIST‑standardised, quantum‑safe key encapsulation mechanism.
Translation: Signal is actively becoming quantum‑resistant, not someday — now.
Signal Protocol and Post-Quantum Ratchets
Real‑world quantum‑safe deployments like this should reassure everyone watching the space.
Europe’s Quantum Moment
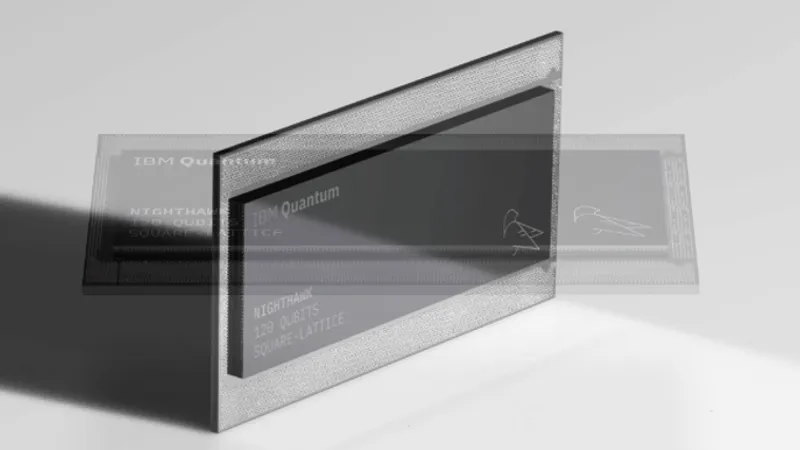
The Basque Government recently unveiled Europe’s first IBM Quantum System Two, powered by a 156‑qubit IBM Quantum Heron processor. This isn’t just a shiny chrome cylinder — it’s a sign that Europe is investing heavily in quantum capability.
The global race is well underway and the number of quantum systems increasing.
What You Should Do Next
Here’s the simple, practical checklist:
✔ 1. Build your PQC migration plan
Identify systems that rely on classical encryption and map out when and how they’ll transition. Simply track them and take action if required.
✔ 2. Prioritise bespoke or legacy systems
These carry the most risk. Get a game plan either decommission, re-develop or upgrade.
✔ 3. Track vendor roadmaps
Most major suppliers are already migrating. Make sure you’re aligned.
✔ 4. Assume your historical stolen data is at risk
Classify and protect accordingly. Get yourself a plan for the worst case scenario.
✔ 5. Stay close to NCSC guidance
They’re publishing excellent, practical recommendations.
Final Word
Quantum computing isn’t a doomsday event — it’s a countdown. Organisations that prepare now will transition smoothly. Those that wait will be playing catch‑up against adversaries armed with new tools. You’re just on a journey. And now’s the time to take the next step.
About IT Security Locksmith
IT Security Locksmith specialises in board level training and consultancy.
To find out more about our capabilities please click here.
Our services page showcases the types of services we offer.
Click here to contact us for a no obligation initial consultation.
